experiments in sound, silicon chips and voice — 1m2lab
Statement: Users should have the right to control their own devices
The problem with smart home devices is not the technology.
The problem is control.
An increasing number of consumer devices are designed to function only through the manufacturer’s cloud service. This is not a technical necessity — it is a business model.
A model where:
- the user does not control their own data
- the basic functionality of the device depends on external servers
- the lifespan of the device is determined by a company’s business decisions
- local control is deliberately prevented
The Tuya ecosystem strongly represents this model.
This project is a deliberate counter‑statement to that development.
This is not piracy, circumvention for malicious purposes, or an attempt to harm the manufacturer.
This is ethical hacking.
Technical knowledge used to restore something that rightfully belongs to the user: control.
“If a device only works through the cloud, the user does not own it — they rent it.”
Why Tuya Cloud is a Security Risk
In Tuya‑based devices, the cloud is not an optional feature — it is the control center.
Data Location
Tuya uses global infrastructure including servers located in China.
Users do not have a clear understanding of where their data is processed.
Metadata is More Valuable than Content
Device metadata can reveal:
- when you are home
- when you are sleeping
- when you press buttons
- when doors are opened
Cloud Dependency
If the service is shut down, sold, or converted into a paid service, the device may become useless.
Closed Ecosystem
Manufacturers decide:
- which integrations are allowed
- which APIs are exposed
- when support ends
Local Network Bypass
Even when devices and controllers are on the same LAN, traffic is often routed through the internet.
Using local Zigbee + Home Assistant eliminates these risks entirely.
Ethical Hacking Case Study
Device
Nedis Zigbee WiFi Gateway (WIFIZB10WT)
Converted into a fully local Zigbee coordinator without Tuya cloud using:
- OpenBeken (WiFi MCU)
- EFR32MG13 / TYZS3 (Zigbee MCU)
- ZHA (Zigbee Home Automation in Home Assistant)
- EZSP over TCP
Result:
- fully offline Zigbee network
- no vendor cloud
- no USB dongle
- full local control
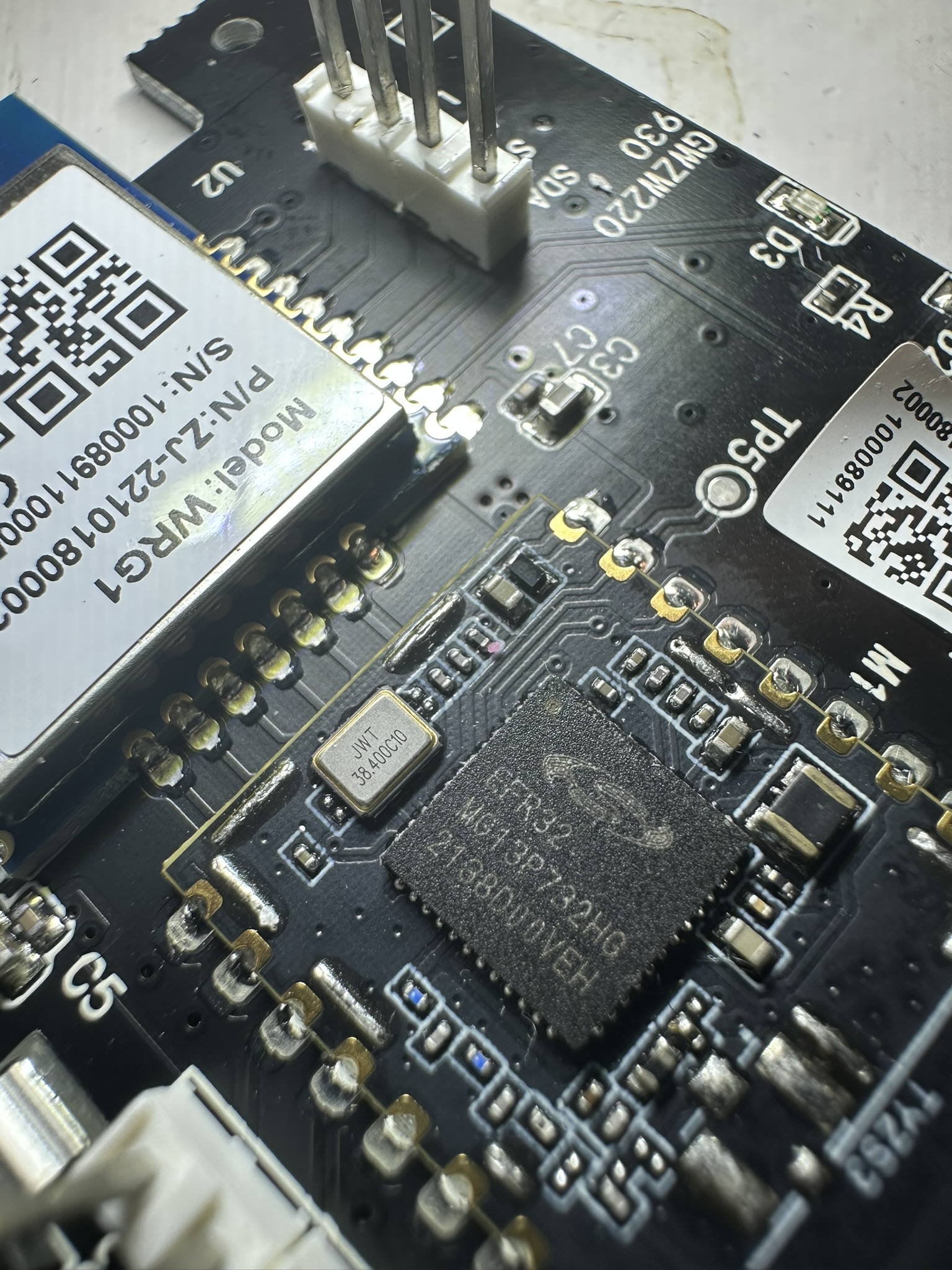
Hardware Overview
Gateway: Nedis WIFIZB10WT
WiFi MCU
RTL8710A (OpenBeken)
Zigbee MCU
EFR32MG13P732 (TYZS3 module)
Interface
UART (TX / RX / GND)
Debug
SWD (J‑Link)
Architecture
Zigbee Device
↓
EFR32MG13 (EZSP NCP firmware)
↓ UART
RTL8710A (OpenBeken uarttcp)
↓ TCP 8888
Home Assistant (ZHA)ZHA connects via:
tcp://<gateway_ip>:8888OpenBeken autoexec.bat
Installed via the OpenBeken WebUI.
startdriver uarttcp 115200 512 1 0
SetChannelLabel 1 "Bridge Connection"
SetChannelVisible 1 0
SetChannelType 1 OpenClosed_InvWhat it does
- starts UART ↔ TCP bridge
- listens on TCP port 8888
- uses correct EZSP baudrate 115200
- disables flow control
Common Pitfall: swflow ≠ XON/XOFF
Some guides say:
“replace last symbol with 0 if you flashed swflow firmware”
This often causes confusion.
Important clarification
Even though the firmware name contains swflow, it:
- does NOT mean UART software flow control
- does NOT use XON/XOFF
- does NOT use RTS/CTS
EZSP manages its own buffers.
Correct configuration:
startdriver uarttcp 115200 512 1 0| Value | Meaning |
|---|---|
| 0 | correct – no flow control |
| 1 | wrong – XON/XOFF |
ZHA Configuration
When adding the Zigbee Home Automation integration in Home Assistant:
Radio type:
EZSPSerial device path:
tcp://<gateway_ip>:8888Port speed:
115200Note: the baudrate value is required but unused over TCP.
Result
- ZHA connects successfully
- Zigbee network runs locally
- devices pair normally
- no Tuya cloud
- no vendor lock‑in
First test device:
Nedis Zigbee Smart Button ZBWS10WT — paired successfully.
Summary
This project demonstrates that cloud‑centric Zigbee gateways can be:
- opened
- converted to fully local devices
- integrated into open smart home ecosystems
All while remaining transparent, documented and ethical.
Sources
Mozilla Foundation – Privacy Not Included: Tuya Smart
https://foundation.mozilla.org/en/privacynotincluded/tuya-smart/
The Markup – Does Your Smart Device Send Data to China?
https://themarkup.org/ask-the-markup/2021/02/10/does-your-smart-device-send-data-to-china
EFF – Internet of Things and Surveillance
https://www.eff.org/deeplinks/2020/12/internet-things-and-surveillance
NIST – Managing IoT Cybersecurity Risks
https://www.nist.gov/publications/considerations-managing-internet-things-cybersecurity-and-privacy-risks
Home Assistant – Local Control Philosophy
https://www.home-assistant.io/docs/
Elektroda – TYZS3 Zigbee NCP Conversion Guide
https://www.elektroda.com/news/news4130211.html